Enabling Anyone To Verify Anything
With the power to share information securely without exposing the underlying data, Origin Secured’s unique Trust Engine technology transforms how people and organisations interact.
Origin Secured is not here to fix trust in systems; we are here to reshape how the world trusts
Trust Without Exposure
Proving identity, compliance, and authority without exposing underlying data.
Origin Secured redefines trust across digital interactions by enabling individuals or organisations to share verified credentials securely, without exposing underlying data. Our Trust Engine technology creates an environment in which identity, compliance, and permissions can be confirmed instantly through cryptographic proof.
Moving beyond static logins, passcodes, and siloed databases, Origin Secured establishes a Unified Digital Presence that allows credentials to be proven dynamically at the point of action. This ensures that trust is based on verified authority, not assumptions.
The result is a privacy preserving, tamper evident framework for secure credential verification that reduces risk, strengthens security, and builds confidence across every part of your digital ecosystem.

Our technology enables verification, without disclosure:
Credential Challenge: Verify workforce credentials through a secure credential challenge without exposing sensitive data, protecting both organisations and their people.
Workforce Readiness: Improve operations by verifying workforce credentials, access permissions, skills, training, and readiness instantly, at the point of action.
Supply Chain Illumination: A company can demonstrate it holds valid insurance, licenses, or compliance certifications, endorsed by the issuing authority, without exposing unrelated corporate data.
Immutable Proof: The unique OS Event Chain is a black box recorder for digital interactions; every event is cryptographically signed so it cannot be altered, meaning every interaction is verifiable and tamper-proof, without exposing an entity’s data.
At the heart of our approach is decentralised, portable verification. Each endorsement is independently verifiable, and control stays with the entity; they decide what to share, when, and with whom.
With Origin Secured, proof is separated from data; protecting privacy, reducing compliance risk, and enabling trust to scale across end-end operations.

Use Cases
Origin Secured’s Trust Engine technology solves challenges with secure sharing information and increasing trust across a workforce, a value chain, or asset inventory. Discover more about Origin Secured’s use cases and how they may apply to your organisation.
Enhance Security, Elevate Compliance, and Increase Efficiency
Origin Secured's ground-breaking Credential Challenge solution is designed to streamline onboarding, increase compliance, and safeguard your operations. Empower your workforce and enable trusted interactions with secure, verified credentials.
Key Benefits:
Reduced risk of identify and credential fraud
Simplified employee onboarding and secure access management
Automated credential checks to verify authorisation at the point of action
Streamlined adoption, augmenting existing systems
Origin Secured strengthens trust and operational efficiency across any industry.

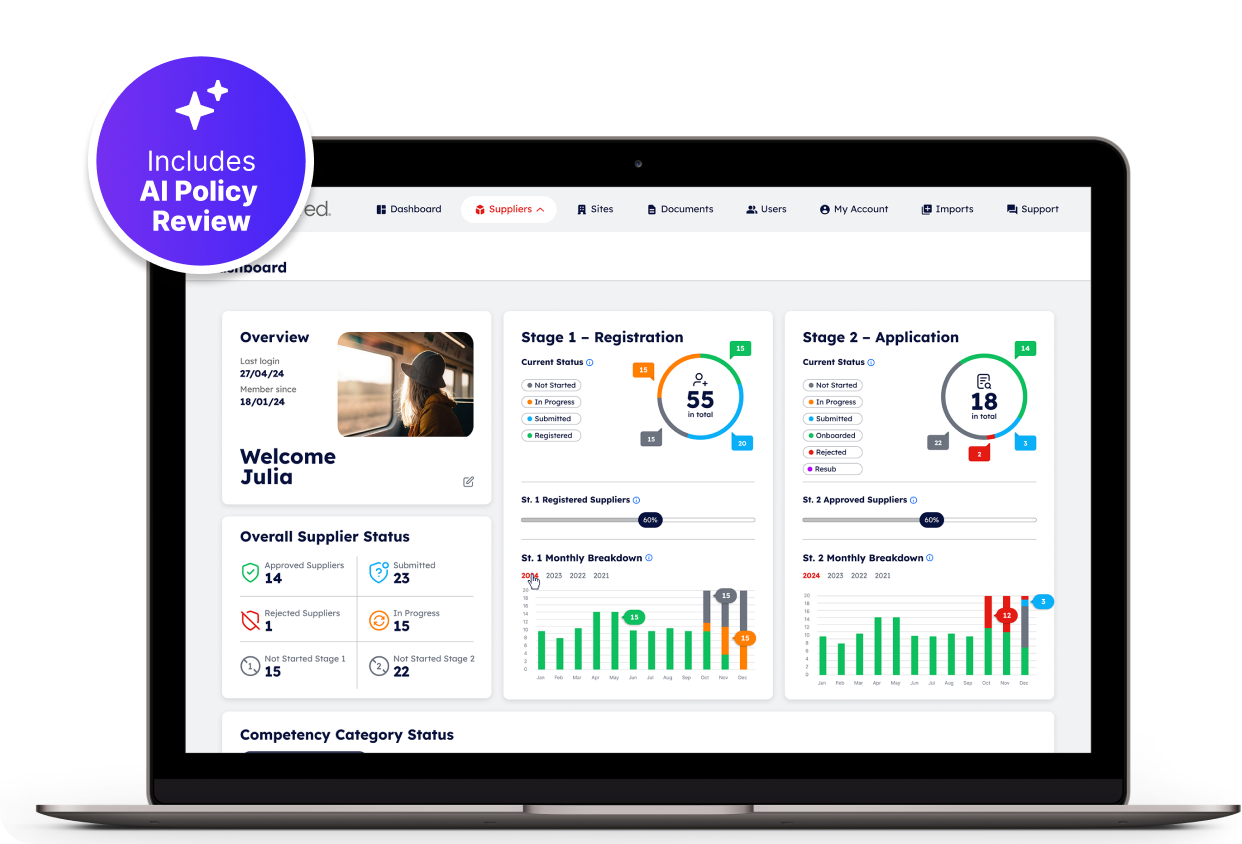
Reduce Supplier Risk, Improve Visibility, And Boost Efficiency
Managing supplier relationships effectively is critical to protecting your business and maintaining compliance. OS Supply Chain Illumination is tailored to help you reduce risks, save time, improve visibility and enhance efficiency in supplier management.
Our platform automates the following activities:
Onboard And Manage Your Workforce With Ease
Managing the onboarding of your workforce doesn't have to be complicated or costly. OS Workforce Readiness will streamline your procedures, minimise cost, increase security, and mitigate risks.
Our platform automates the following activities:

Our Mission
Origin Secured is on a mission to increase trust in the information shared between people and organisations through innovative technology; simplifying verification and restoring trust with a suite of interoperable tools that protect your underlying data.
Accreditations
